REST API vulnerabilities
Looking for REST API vulnerabilities
API vulnerabilities are common entry points for exploitation. OWASP API Top 10 compiled list. We have to explore for all the cases to see if there is any vulnerability.
Exploration 1
In one of the above sections, we explored view balance API.
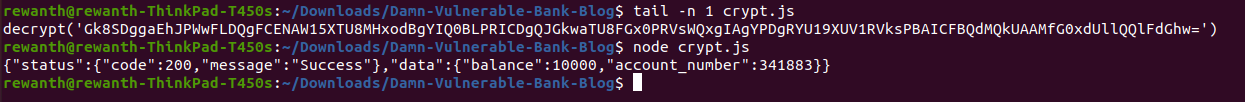
decrypt("Gk8SDggaEhJPWwFLDQgFCENAW15XTU8MHxodBgYIQ0BLPRICDgQJGkwaTU8FGx0PRVsWQxgIAgYPDgRYU19XUV1RVksPBAICFBQdMQkUAAMfG0xdUllQQlFdGhw=")
Let's see if we can view balance of other users. If you see the intercepted request, there is no body or query string in the request made to view balance. But we can see the Authorization header.
In my case, the authorization header is eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VybmFtZSI6InVzZXIxIiwiaXNfYWRtaW4iOmZhbHNlLCJpYXQiOjE2MjMzMzU4NDV9.lHjjBagQ2OYREBBDl0LXUNLNn1nD6nI4KMxgFlfXRWU. This looks like JWT token. Let's decrypt this JWT token.
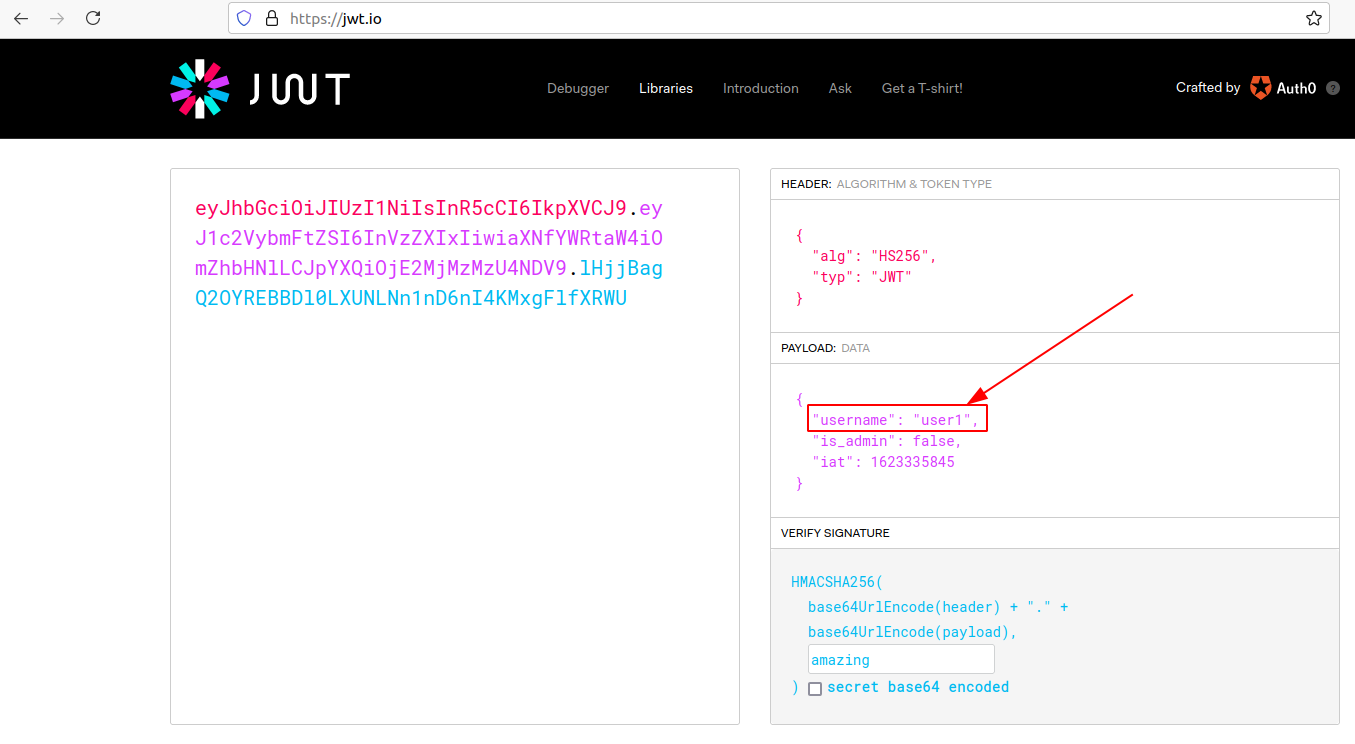
As you can see we have a field name "username":"user1". Since there is no body/query parameter in the intercepted request, there is high possibility that the application is extracting username from the authorization header. Let's change the username to user2, rebuild the request and then send it.
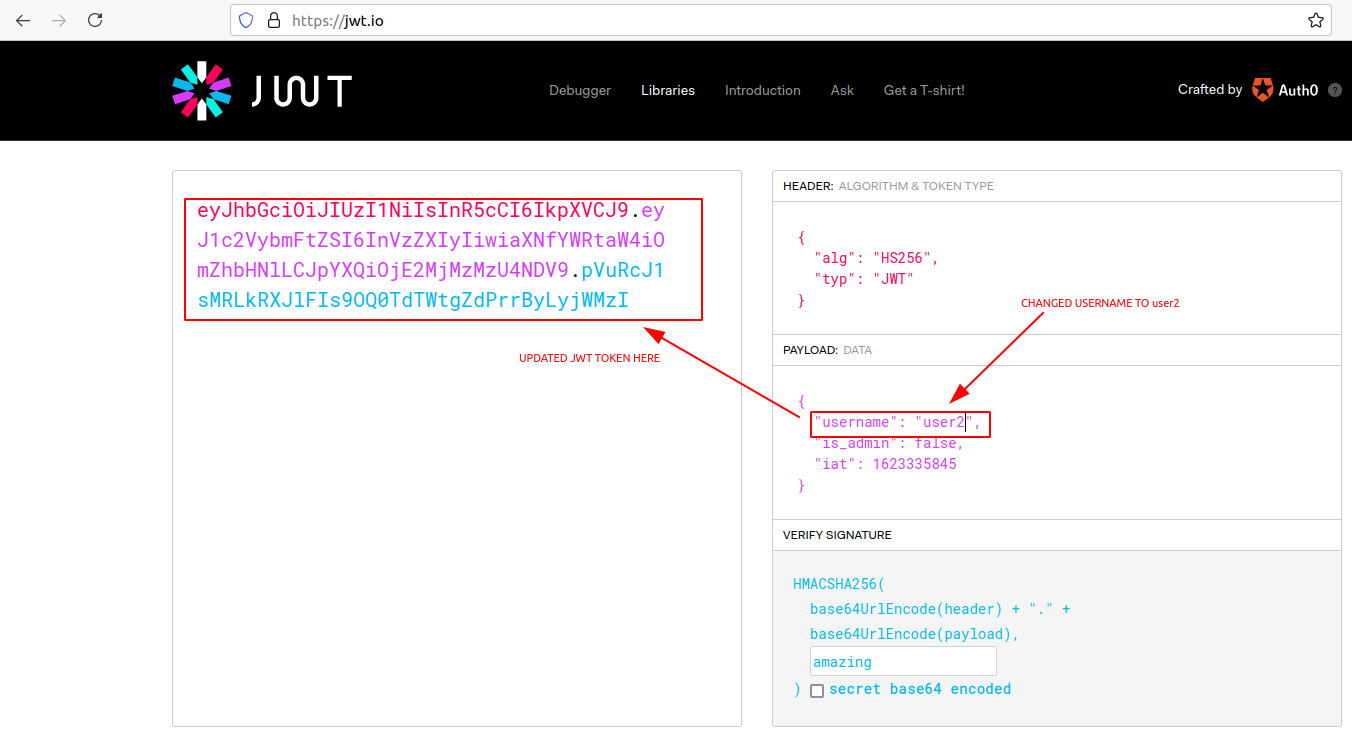
Copy this JWT token and replace the Authorization header with this value and resend the request.
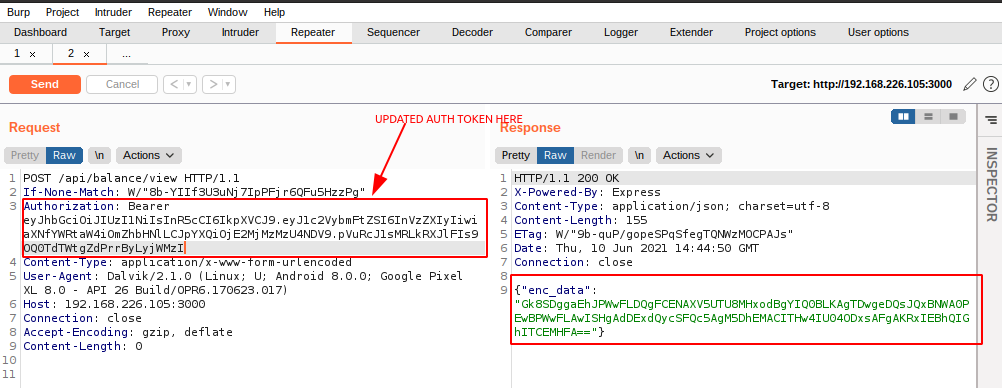
We will receive an encrypted response, copy that and pass it to your NodeJS script for decryption.
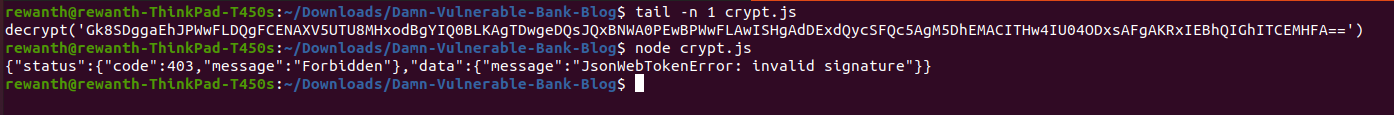
As we can see above, it throws 403 error and says the signature doesn't match. It means the signature is getting validated on the backend and we can't tamper with the Authorization token. It doesn't mean authorization is happening in all endpoints. It might happen, it might not happen, as a security expert its your job to verify them all.
Similarly you can explore the remaining scenarios.
Created: 2021-07-02 22:22:26